4.3.1.2 Factory Reset (Immutable Recovery Image)
In the case of a factory Reset, an OTP Flash region can be used to create region of memory that is protected from both erase and write operations, even from IRT code. Because OTP regions cannot be unlocked, their permissions are locked on Reset. If the OTP region is configured with writes disabled, then both writes and erases are disabled.
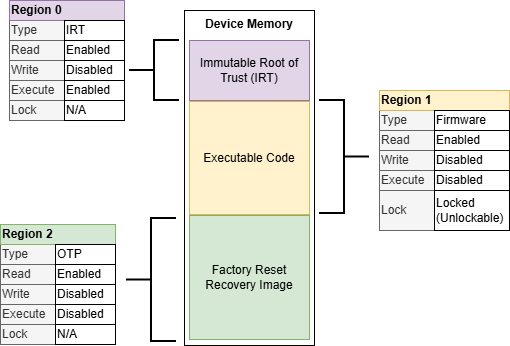
In Figure 4-19, the factory reset image is not executable and is copied into the executable memory region for the recovery. This means if the compromised image is going to be analyzed, it must be read out before the system can recover.
An alternative solution could be to allow the system to run the factory image directly from the factory reset recovery image. In this case, the OTP section is made executable, and the factory image can always be run after Reset.
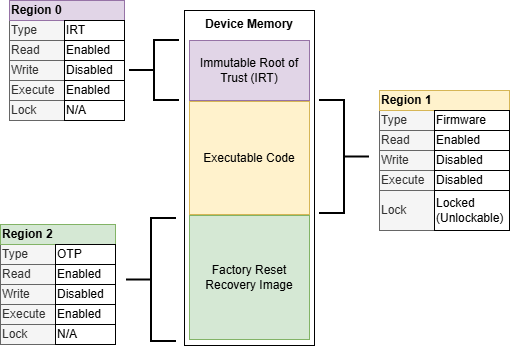
In this case, the factory reset recovery image will require different linking/building configuration to target execution from a different memory space. The boot code also needs to know how to transfer control to this section memory region, including remapping the interrupt vector table.
In many cases, a factory reset recovery image should be only used for a short period of time until a full recovery can be completed to the latest version. The factory reset recovery image may contain vulnerabilities or function issues that have been addressed in newer versions. Vulnerabilities might be severe enough to need to quarantine the system until updates are provided.
In a system that requires authorization for recovery, extracting the corrupted image for analysis could be included as part of the recovery operation. This diminishes the benefit of having the factory reset recovery image runnable in place. In a system that is allowed to automatically recover, having a factory reset recovery image that is executable in place may allow the system to recover while maintaining the corrupted image for analysis. A system that can only recover to a factory image rather than a last known good version might not want to allow automatic recovery.
The keys used to authenticate the signature of a recovery image need to be considered. This is particularly important for a factory reset image if it is a fixed image in OTP memory. If the keys used to sign the factory image are revoked or replaced, then the system might not be able to authenticate the factory image. If key rotation and key revocation are in use, then having a factory Reset in OTP needs to weigh the possibility of the compromise of the factory reset signature keys. This may render the immutable factory Reset unbootable. A mutable recovery scheme could be used for a factory Reset in this case to replace the factory reset recovery image with a new factory reset recovery image with a new signature in the case of a key compromise rather than an OTP factory Reset.
The integrity and authenticity of the factory reset recovery image can be verified using the Cryptographic Accelerator Module (CAM) using the same methods described in Secure Boot and Secure Firmware Update. Alternatively, given the memory is OTP, a system could inherently trust this memory given it is not modifiable.
Key Considerations:
- A recovery plan should consider supporting the extraction of a corrupt image for analysis. This decision could impact the way the device is configured or the way updates are downloaded and/or installed.
- Flash protection regions can be used to protect recovery images from modification during normal operation until authorized to update the recovery image.
- OTP regions can be used to create immutable factory reset points.
