4.2.1.2 Firmware Update Image
Security Objectives:
- Authenticity
- Integrity
- Access Control
- Authorization
During a secure firmware update, the incoming firmware image becomes an asset of the system. Before the download of a new image even starts, the existing image in the download scratchpad could be considered an asset as well. This download scratchpad might be used as a backup of the current image for recovery situations.
During a new image download, it is important to restrict execution permissions to the incoming image until it is verified and authenticated. Creating a separate Flash protection region for the download scratchpad and disabling code execution during the download allows the device to restrict access to execution until the image is verified and installed.
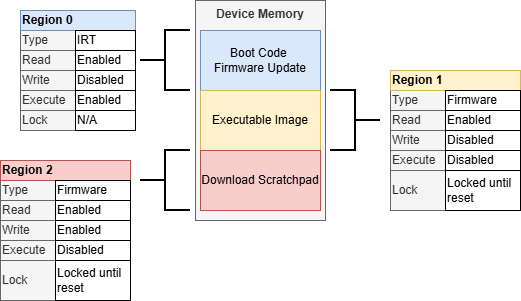
Figure 4-12 demonstrates a download scratchpad region that is blocked from execution until its integrity and authenticity can be verified.
Once the download is complete, the image integrity and authenticity need to be verified before installing the new image, even if that installation is just changing a memory pointer to allow it to run. During the download verification, the existing executable image can be protected from edits. Additionally, the download scratchpad should be limited to modification and execution until the verification and installation processes are complete. During this image evaluation phase, other update rules might be checked such as anti-rollback protection.
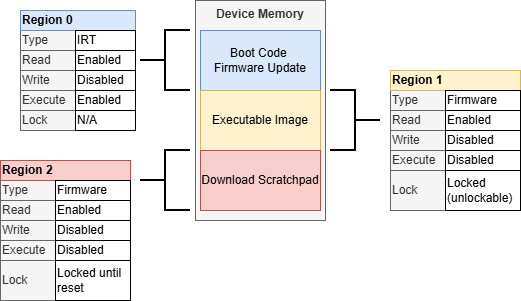
During the download verification process before installing the new image, the download image integrity and authenticity are verified. During this process, writes to the download image and existing code image need to be protected. Execution of the new image should also be restricted until the verification and installation are complete.
During the new image installation, the download scratchpad can remain protected from writing to protect the image during the installation process. The executable image space needs to be made writable so that the new image can be installed. During the installation, execution should be blocked until the installation is verified. The download image is write-protected to prevent corruption of the verified/authenticated new image.
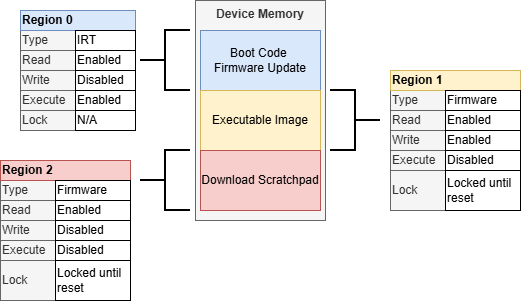
Finally, once the installation is complete, the newly installed image can be verified and authenticated during the standard boot process.
The lock-until-reset feature is used several times while updating a firmware image to prevent unintentionally unlocking regions during each of the phases of a firmware update. This requires a Reset to move on to the next firmware update/boot phase. The status of a firmware update can often be determined by the states and versions of the firmware images themselves but can be simplified using the IRTSTAT register as described in IRTSTAT.
In systems where the download scratchpad is used as a recovery point, protecting it from intentional corruption might be important. In this case, a system may require an authorization to even allow a new image download to start. This might be something as simple as using a physical presence. It might require a signature that is device specific and tied to the current installed firmware so that the authorization applies to only that device for the specified version of firmware being updated from and to. As seen with other signature-based use cases, the Cryptographic Accelerator Module (CAM) can be used to accelerate these signature verifications.
Key Considerations:
- Consider how the system will recover from a failed firmware update
- Use a dedicated Flash region for a download
scratchpad and limit permission to what is required for the current phase of the
update process
- Keep execution disabled and locked until Reset on the download scratchpad to minimize risk
- Disable writes and execution after the download completes during the image installation process to protect the download scratchpad from modification
- Use a dedicated Flash region for executable code
and limit permission to what is required for the current phase of the update process.
- Disable writes during a firmware update download
- Disable execution and enable writes during an image installation
- Verify the integrity and authenticity of the new installation before enabling execution permissions
- Store keys in IRT Flash regions or other protected regions to ensure they remain immutable and protected from unauthorized modification
