Self Reads
The code’s ability to read program memory is another way that an attacker could attempt to read out the boot code from the device. This attack assumes that the attacker has gained the ability to either load malicious code into the device or has found a means to use the existing code to attempt to read and export the memory. This could also occur if the boot code is developed/installed by a different group than the one developing the first mutable/application code. This might be for IP protection reasons or for security reasons.
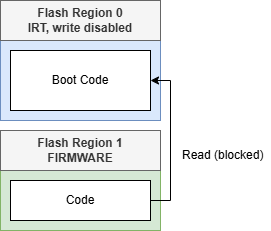
If code running out of a FIRMWARE type Flash protection region tries to read memory from an IRT section, it will cause a memory exception and block the read. A properly configured IRT section will block this type of access attempt as well as block write and flow control changes between the two regions. This requires that the IRT region correctly configure and exit IRT mode before handing control to the non-IRT FIRMWARE region. Immutable Root of Trust (IRT) Region Features and Usage describes how to configure and exit an IRT section.