Code Signature Verification Also Needed In Firmware
If FIRMWARE code needs to authenticate another stage of code (e.g., code loaded into RAM), then a code signing key needs to be accessible to the FIRMWARE version.
If the firmware loaded by the IRT/boot also wants to verify code signatures of next stage code/data, then it also needs access to code signing keys. If the code signing keys are stored in the IRT section, then this is inaccessible by the firmware. IRT sections are read-protected from non-IRT sections.
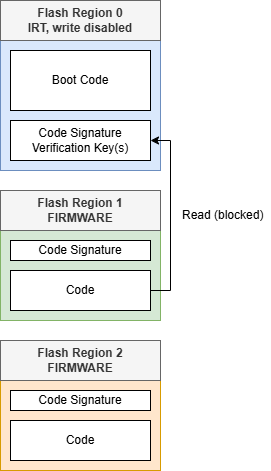
In Figure 4-3, the boot code has loaded the FIRMWARE in Region 1. This firmware wants to authenticate and run the code in Region 2. The key stored in the IRT is inaccessible. Reads from a non-IRT section to an IRT section are blocked.
If a system needs to create a deeper chain of trust, and the system does not plan to support updating keys, then the key store can be placed in a write-protected OTP section. This protects the immutability of the keys while allowing them to be accessible by both the IRT and FIRMWARE sections.
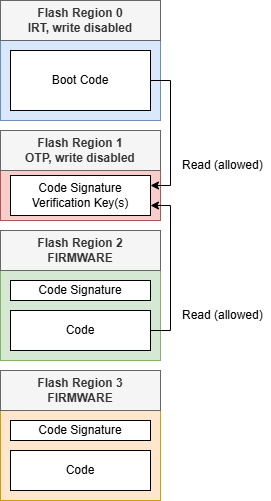
As shown in Figure 4-4, an OTP region with writes disabled is used to store fixed code signature verification keys that are immutable but accessible from both the IRT and non-IRT code.
Configuring Region 1 as an OTP, Write-Protected Section (One Flash Page in Size)
// FPR1CTRL
#pragma config FPR1CTRL_RDIS = OFF //Region protection enabled
#pragma config FPR1CTRL_EX = OFF //Execute permission disabled
#pragma config FPR1CTRL_RD = ON //Read permission enabled (if needed)
#pragma config FPR1CTRL_WR = OFF //Write permission disabled (mutable data)
#pragma config FPR1CTRL_RTYPE = OTP //Region type: One-time programmable
#pragma config FPR1CTRL_PSEL = BOTH //Partition Select: Both Panels
// FPR1ST
#pragma config FPR1ST_START = 0x10 //Region start address bits
// FPR1END
#pragma config FPR1END_END = 0x10 //Region end address bitsIn a system of this complexity, having an updatable key store instead of using immutable keys should be considered to handle the possible case of a key being compromised.
Key Consideration:
- Properly configured IRT regions will block reads from non-IRT regions. If fixed data needs to be shared between IRT and non-IRT regions, consider an OTP region with writes disabled.
