1.21 TCP/IP WolfSSL TCP Client
This configuration demonstrates creating an Internet client that uses the MPLAB Harmony TCP API to create a TCP/IP connection to a Web server. The connection can either be clear text, or it can use TLS to encrypt the connection with wolfSSL. The demonstration uses IPv4. (But it can use either IPv4 or IPv6)
This demonstration uses the NET_PRES layer for encrypted communication through an external service provider for TLS support.
TCP/IP WolfSSL TCP Client MCC Configuration
The following Project Graph diagram shows the Harmony components included in the WolfSSL TCP Client demonstration application.
MCC is launched by selecting Tools > Embedded > MPLAB® Code Configurator from the MPLAB X IDE and after opening the project, TCP/IP demo project is ready to be configured and regenerated.
TCP/IP Root Layer Project Graph
The root layer project shows that USART1 peripheral is selected to do read and write operation for TCP/IP commands.
This is the basic configuration with SYS_CONSOLE, SYS_DEBUG and SYS_COMMAND modules. These modules are required for TCP/IP command execution.
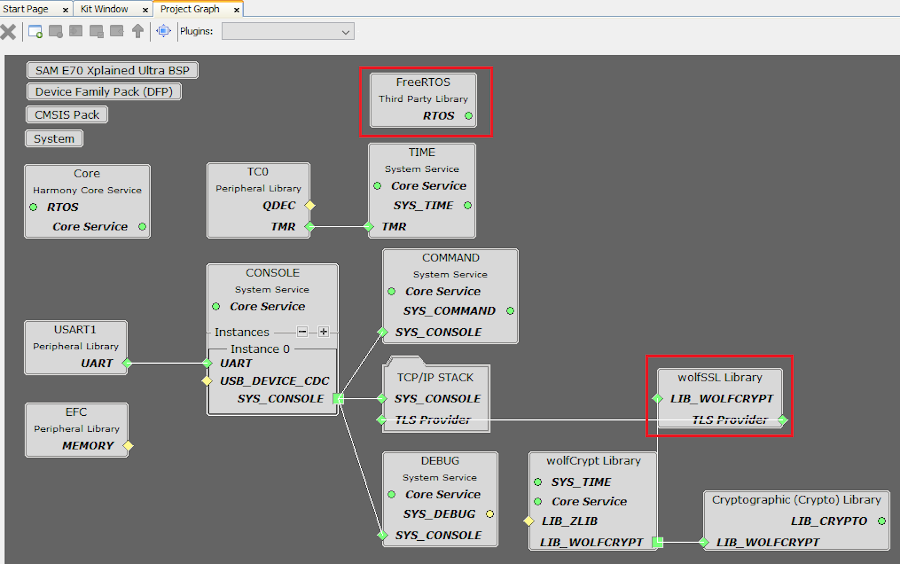
NOTE:-
FreeRTOS component is required for RTOS application. For bare-metal (non-RTOS) FreeRTOS component should not be selected.TCP sockets calculate the ISN using the wolfSSL crypto library.
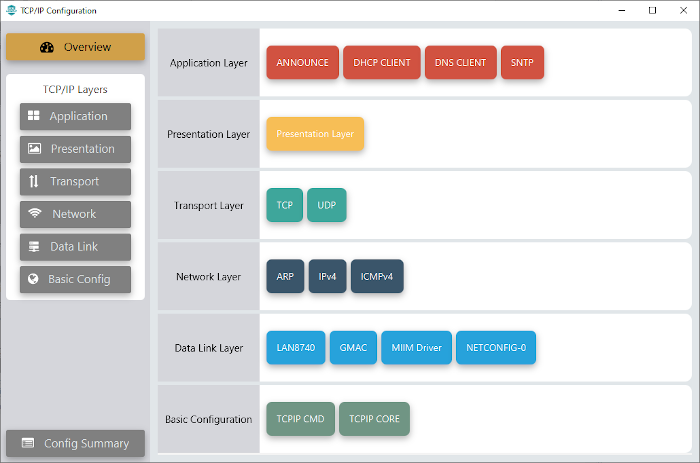
TCP/IP Configuration
- SAM E70 Xplained Ultra
- SAM E70 Xplained Ultra
TCP/IP Required Application
TCP/IP demo use these application module components for this demo.
Announce module to discover the Microchip devices within a local network.
DHCP Client module to discover the IPv4 address from the nearest DHCP Server.
DNS Client provides DNS resolution capabilities to the stack. During these components selection, the required transport and network modules are also selected.
SNTP Simple Network Time Protocol updates its internal time periodically using a pool of public global time servers.
TCPIP Data Link Layer
Internal ethernet driver(gmac) is enabled with the external LAN8740 PHY driver library for SAME70 demonstartion.
The MIIM Driver supports asynchronous read/write and scan operations for accessing the external PHY registers and notification when MIIM operations have completed.
TCP/IP WolfSSL TCP Client Hardware Configuration
This section describes the hardware configuration for ATSAM E70 Xplained Ultra Evaluation Kit and one can be used for the respective application demonstration.
This section describes the required default hardware configuration use SAM E70 Xplained Ultra Evaluation Kit
Ensure ERASE jumper is Open.
Open the J805 Jumper
Refer to the SAM E70 Xplained Ultra User Guide
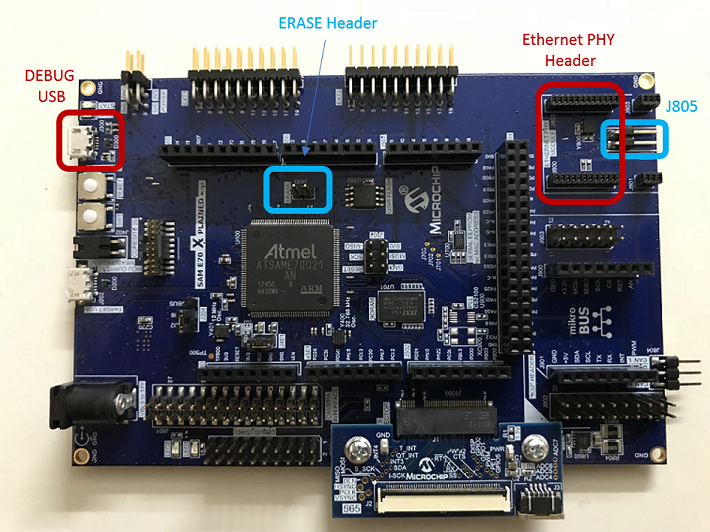
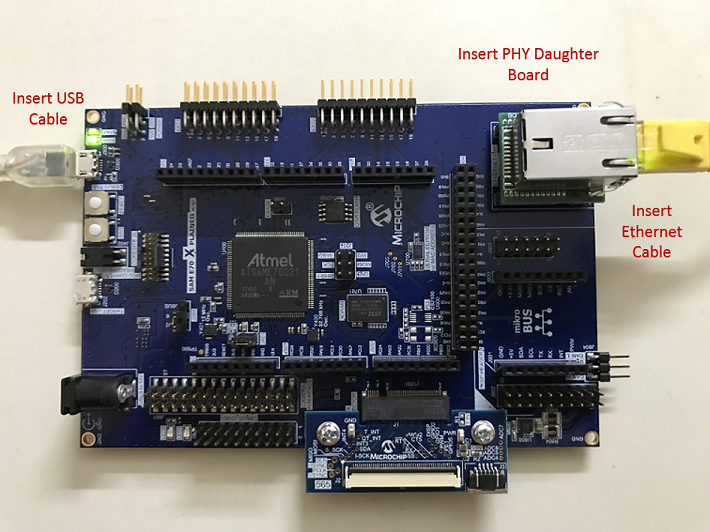
Insert the LAN8740 PHY daughter board on the ETHERNET PHY MODULE header.
Connect the micro USB cable from the computer to the DEBUG USB connector on the SAM E70 Xplained Ultra Evaluation Kit
Establish a connection between the router/switch with the SAM E70 Xplained Ultra Evaluation Kit through the RJ45 connector
TCP/IP WolfSSL TCP Client Running Application
This table list the name and location of the MPLAB X IDE project folder for the demonstration.
| Project Name | Target Device | Target Development Board | Description |
|---|---|---|---|
| sam_e70_xult.X | ATSAME70Q21B | SAME70 Xplained Ultra + LAN8740 PHY Daughter board | Demonstrates the wolfSSL TCP Client on a development board with ATSAME70Q21B device and LAN8740 PHY daughter board. This is a bare-metal (non-RTOS) implementation. WolfSSL Hardware crypto enabled |
| sam_e70_xult_freertos.X | ATSAME70Q21B | SAME70 Xplained Ultra + LAN8740 PHY Daughter board | Demonstrates the wolfSSL TCP Client on development board with ATSAME70Q21B device and LAN8740 PHY daughter board. This implementation is based on Freertos. |
| sam_e70_xult_sw.X | ATSAME70Q21B | SAME70 Xplained Ultra + LAN8740 PHY Daughter board | Demonstrates the wolfSSL TCP Client on a development board with ATSAME70Q21B device with and LAN8740 PHY daughter board. This is a bare-metal (non-RTOS) implementation. WolfSSL Software crypto enabled |
Running Demonstration Steps
Build and download the demonstration project on the target board.
If the board has a UART connection:
A virtual COM port will be detected on the computer, when the USB cable is connected to USB-UART connector.
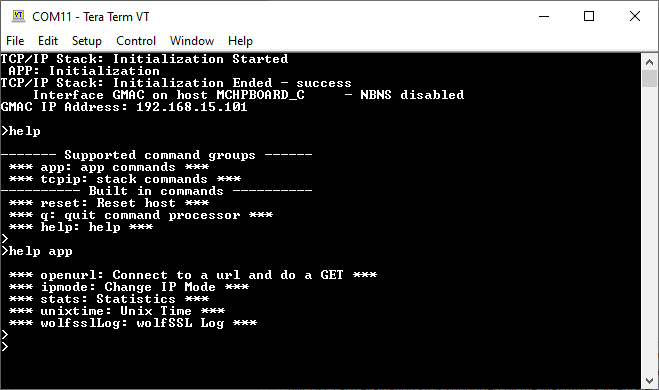
Open a standard terminal application on the computer (like Hyper-terminal or Tera Term) and configure the virtual COM port.
Set the serial baud rate to 115200 baud in the terminal application.
See that the initialization prints on the serial port terminal.
When the DHCP client is enabled in the demonstration, wait for the DHCP server to assign an IP address for the development board. This will be printed on the serial port terminal.
Alternatively: Use the Announce service or ping to get the IP address of the board.
Run tcpip_discoverer.jar to discover the IPv4 and IPv6 address for the board.
Execution :
As soon as a valid IP address is assigned through the DHCP to the demonstration, it is ready to accept console commands.
There are three commands available in the demonstration from the serial port:
- openurl < url > - The < url > argument must be a fully formed URL; for instance, http://www.microchip.com/
- ipmode < mode > - The < mode > argument selects the IP version. 0 - Any IP version, 4 - IPv4 only, 6 - IPv6 only
- stats - Output the statistics of the previous openurl run. Statistics such as how long each phase of the connection took, and how many bytes were transferred.
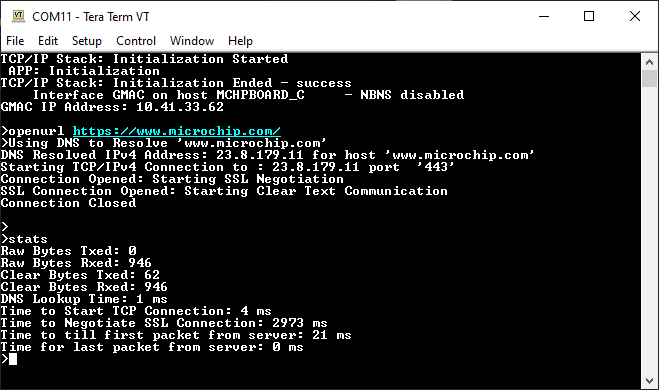
After the successful board bring up, the console output becomes
TCP Client Test
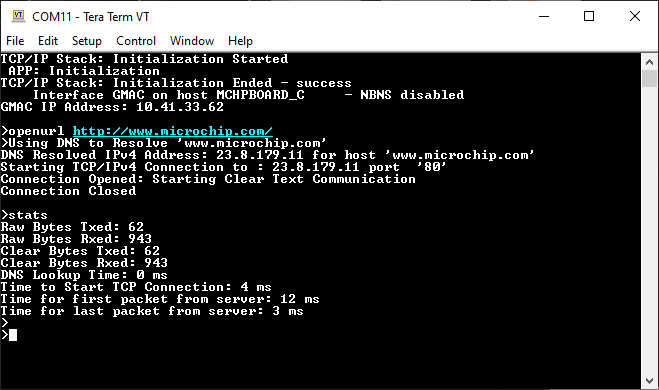
a. Clear text connection (Port 80):
Enter following command in console: openurl < url >. For example, openurl http://www.microchip.com/ , the connection established here is clear text.
By entering the command stats, the response is obtained as shown below.
The response from the server will be printed on the console as shown below.
The expected output -
b. Encrypted connection (Port 443):
Enter following command in console: openurl < url >. For example, openurl https://www.microchip.com/ , the connection established here is encrypted connection with wolfSSL.
The response from the server will be printed on the console as shown below.
By entering the command stats, the response is obtained as shown below.
The expected output -